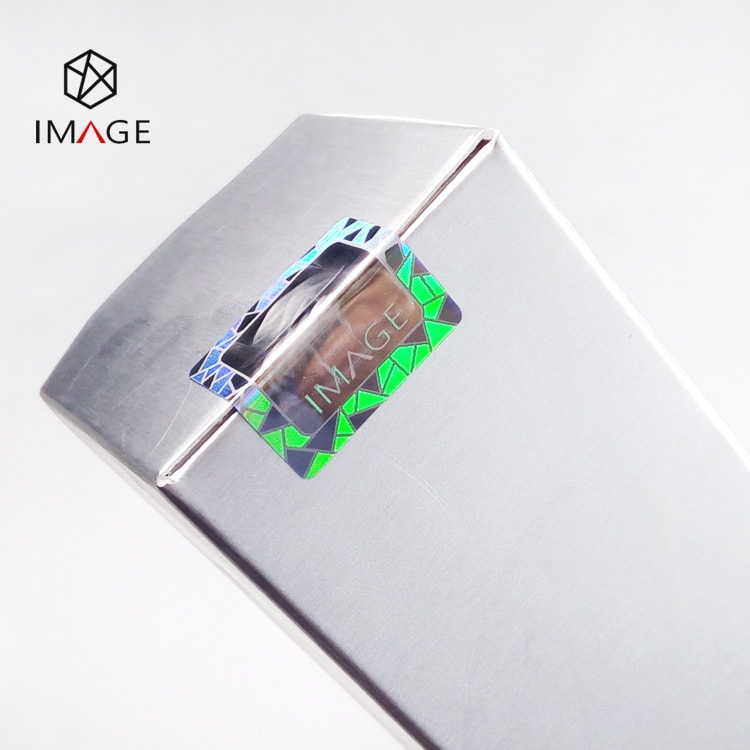
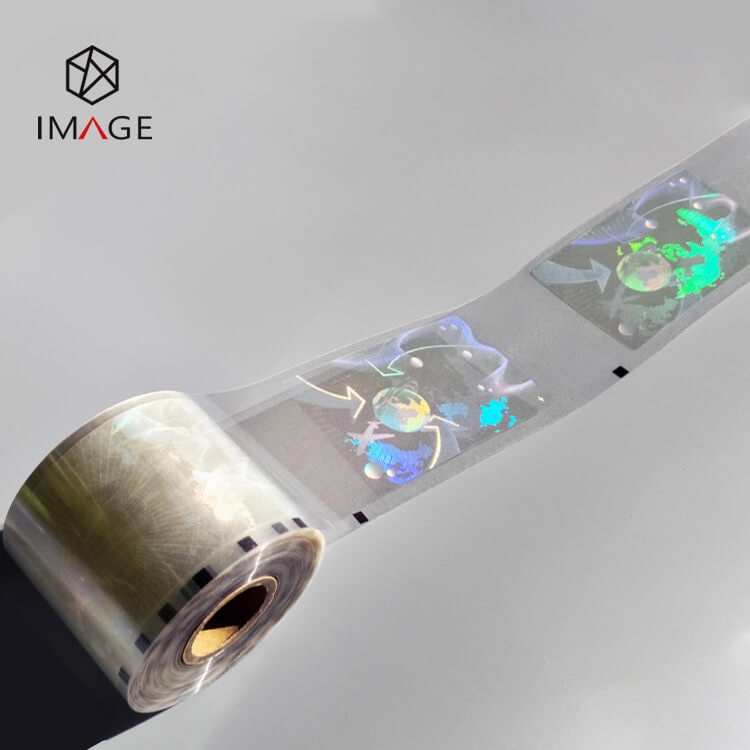
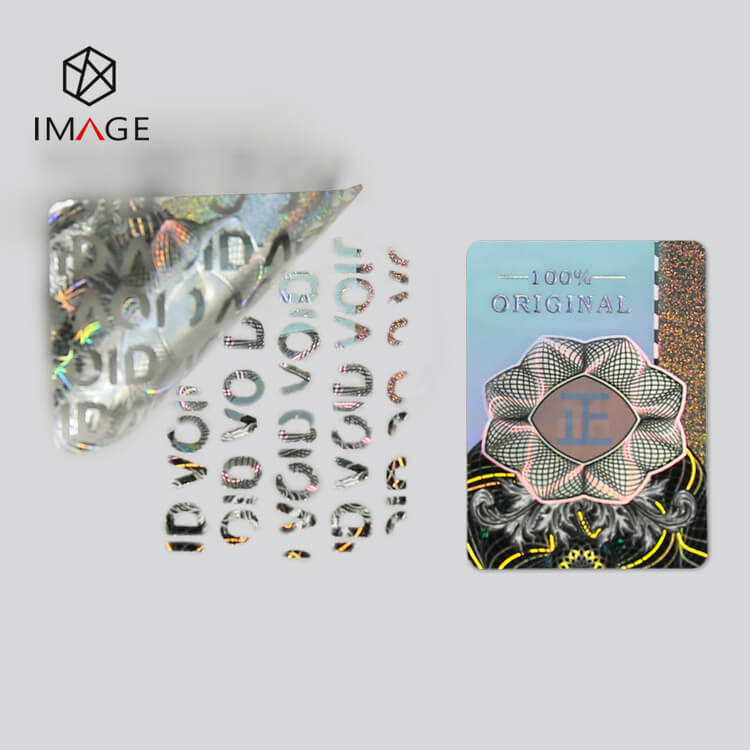
Sailboat Hologram Cold Laminate Overlay
The sailboat pattern hologram cold laminate overlay is available to work with varieties of plastic ID card substrates, including PVC, PET, PC, etc. The sailboat image presents a rainbow effect, it has beautiful color changes viewed from different angles.